UPDATE D-Link Broadband Routers Vulnerable to DNS Hijack Attack
A Bulgarian security researcher called Todor Donev has demonstrated a new proof of concept attack against one of D-Link’s ADSL based wireless broadband routers (D-Link DSL-2740R), which allows a hacker to change the routers default Domain Name Server (DNS) details and thus hijack its web traffic. Other routers could also be vulnerable.
The vulnerability has a lot in common with one that was last year revealed to have impacted a huge number different routers (here) and similarly exploits a flaw, using Cross-Site Request Forgery (CSRF) techniques, in the ZynOS firmware used by D-Link and various other router vendors.
In order for the hack to work the attacker needs to be able to reach the web-based admin interface for the router, which is easy enough if the WiFi network is open or if you’re already logged into a related network. But even if the attacker is locked out then the exploit can still be performed by harnessing CSRF to reach the web-based interface (some routers expose their admin interface to the Internet for remote administration).
At this point the attacker can plant malicious code into the user’s web browser, which might occur if they visit a compromised website or bad link. The code then tells the browser to send specially crafted HTTP requests to LAN IP addresses that are usually associated with router (e.g. the admin interface is often accessed via 192.168.1.1 or 192.168.0.1 etc.). If successful then the hacker will gain enough access to change the routers DNS details.
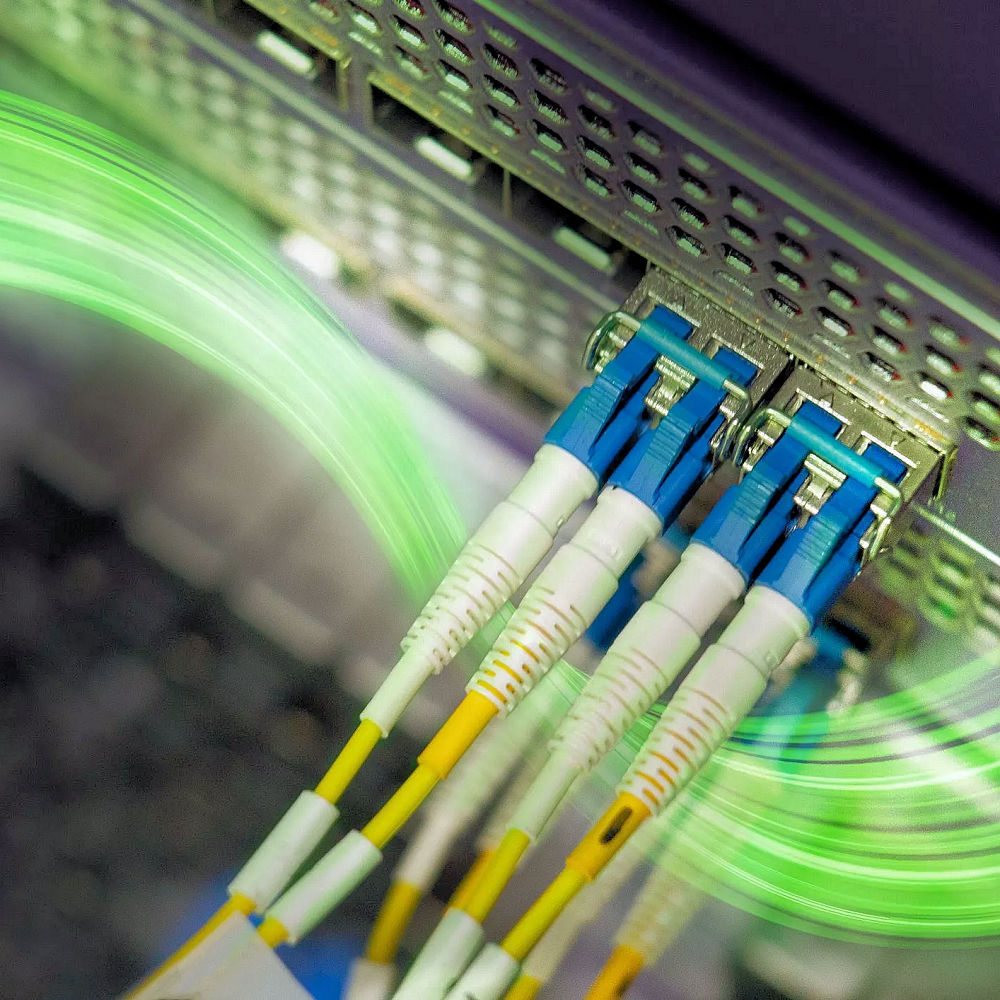
The DNS system works to convert IP addresses to human readable domain names (e.g. 123.56.32.1 to examplefake.com) and back again. Most of the time your ISP will run the DNS servers, but end-users can also access their own computers and routers to use custom domain name systems like OpenDNS or Google’s Public DNS. But if a hacker gains access then he or she can replace the DNS settings with a malicious server to do the same task.
The result of a successful attack means that the hacker can redirect your website requests to fake phishing sites, monitor your activity to steal personal / financial information, inject more exploits into your network so as to gain even greater control and.. well, it’s basically all bad.
Admittedly the router model in question has been phased-out, but lots of consumers use old hardware and router manufacturers are notorious for failing to keep the devices they sell up-to-date and secure. The attack itself has so far only been demonstrated on this one device, but it’s likely that many other router models could be vulnerable, especially given the widespread use of ZynOS.
Several sites have carried this news (example) and all have asked D-Link for a comment, yet so far the manufacturer has not responded. This is arguably the biggest problem with the router industry, the slow pace to respond, identify and address serious exploits in the kit they sell. The past couple of years have been full of similar security flaws.
UPDATE 4th March 2015
Good news, D-Link has finally published a firmware patch for DNS hijacking related vulnerabilities in their DIR-626L, DIR-636L, DIR-808L, DIR-810L, DIR-820L, DIR-826L, DIR-830L and DIR-836L model routers:
http://securityadvisories.dlink.com/security/publication.aspx?name=SAP10052
Mark is a professional technology writer, IT consultant and computer engineer from Dorset (England), he also founded ISPreview in 1999 and enjoys analysing the latest telecoms and broadband developments. Find me on X (Twitter), Mastodon, Facebook and Linkedin.
« BT Extend UK Vectoring Trials to Fix FTTC “Fibre Broadband” Speeds
Latest UK ISP News
- FTTP (5513)
- BT (3514)
- Politics (2535)
- Openreach (2297)
- Business (2261)
- Building Digital UK (2243)
- FTTC (2043)
- Mobile Broadband (1972)
- Statistics (1788)
- 4G (1663)
- Virgin Media (1619)
- Ofcom Regulation (1460)
- Fibre Optic (1394)
- Wireless Internet (1389)
- FTTH (1381)




















































Comments are closed