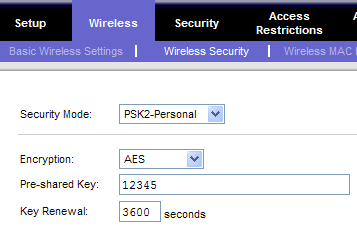
2. Enable WPA Encryption.
Article Index:
This is by far and away the single most important security feature of any wireless network and all but the most isolated networks should be using some form of encryption. However, there are several different types:
WEP encryption is easily the worst of the bunch, due both to its age and the alarming regularity at which it has been hacked. Suffice to say that it is the most vulnerable and should be avoided unless it is your only choice. By comparison WPA and WPA2 are far better options due to having fewer identified vulnerabilities and much stronger encryption, especially WPA2. Encryption is typically defined at the Access Point(AP)/Router level, although the precise location and explanation of how to enable it appears to differ between devices. Once enabled, any client computer connecting to your network will need to type a password (passcode / shared key), as defined by yourself in the wireless options. The picture below shows the encryption related setting on a LinkSys router (note: “PSK2-Personal” really means “WPA2-Personal”):
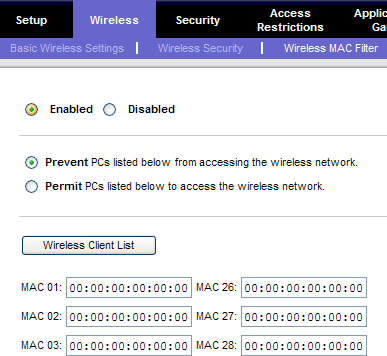
There is only one real side effect to using encryption, which is that it may reduce your maximum transfer speeds and range ever so slightly, depending on the quality of your router. This is a small price to pay for the massive leap in security. 3. Enable MAC Filtering. Not to be confused with Macintosh (Apple) computers or broadband Migration Authorisation Codes, network MAC’s stand for Media Access Control addresses. This is the unique code assigned to every piece of network adaptor hardware (Example MAC: “00:1D:50:65:E6:C7”), which allows the network itself to better identify a connecting device / computer. Most Router/AP’s will offer you the option of MAC Filtering, which as you might expect, lets you limit access to only the network devices you choose. This can also be used in reverse, as a means of banning certain addresses while allowing everybody else:
However, while this may sound like an excellent solution, it does have a number of distinct drawbacks. Firstly, most hackers know how to find the MACs’ your network uses and spoof them, thus circumventing the filter; software to do this is readily available. Secondly, using this method has been known to degrade network performance and may cause connectivity problems, especially on older routers. That being said, if it works - use it, anything extra is helpful.
Have something to say? Check out the ISPreview Forum
http://www.ispreview.co.uk/talk |