UPDATE2 Low Bandwidth DoS Attack Can Hammer Virgin Media SuperHub 3
A growing number of Virgin Media’s cable broadband customers are claiming that the operator’s latest SuperHub 3 (Hub 3.0) router may be vulnerable to a low bandwidth Denial of Service (DoS) attack (i.e. a malicious person with a slow ADSL line could easily ruin your day).
Hopefully by now most of our Virgin Media using readers will be aware that the SuperHub 3 (ARRIS TG2492S/CE) uses a Intel Puma 6 chipset (x86 SoC), which is currently quite notorious due to how it suffers from a tedious bug that causes latency spikes and packet loss (here and here). A fix for this flaw has been in the works for some considerable time but, as we revealed last month, it’s still going through some lengthy testing.
Unfortunately it seems like the situation is about to get worse. Feedback on the DSL Reports site and Virgin Media’s Community Forum appears to show that the hardware is also vulnerable to a simple DoS attack, which means that if somebody knows your Virgin IP address then they could hit you with packets of data (i.e. sending random UDP data to the given host with random destination ports) from even a slow broadband connection and this effectively makes your Internet connection unusable.
Advertisement
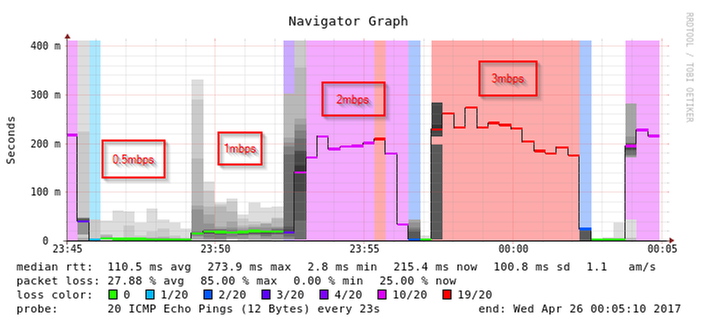
In the example above a 1Mbps DoS causes an average latency rise of +20ms (milliseconds) and quite a few high peaks, while 2Mbps delivers +200ms and a huge amount of packet loss (65%).. it only gets worse from there. The 2Mbps example is enough to ruin most of your Internet activity until the attack stops (sadly you can’t block this one via the SH3’s firewall).
The vulnerability also impacts other routers that use the same Puma 6 chipset. We have asked Virgin Media for a comment and they’ve promised to respond, once their hub and security teams have had a chance to take a closer look. At this point we should remind readers that attacking another Internet user in this way could be considered a criminal offence.
Credits to one of our readers, Dale, for raising the issue. We will update once an official comment arrives and in the meantime The Register has also run a similar story.
Advertisement
UPDATE 12:29pm
According to Ross Allan, who created a piece of software to test the bug, such an attack can’t be stopped by the SH3’s firmwall either because packets from the internet would come through the modem then reach your firewall (i.e. by that point the damage is already done).
UPDATE 4:52pm
Took awhile but Virgin Media has finally given is a comment, although it’s unlikely to satisfy those with concerns.
Advertisement
A Virgin Media Spokesperson told ISPreview.co.uk:
“We take the security and the reliability of our service very seriously and have tools and systems in place on our network to protect our customers. We are currently speaking to our suppliers regarding reports of Puma 6 issues.”
UPDATE 2nd May 2017
Netgear has published a related Security Advisory for their Puma 6 supporting CM700 cable modem kit, which appears to confirm the issue.
Netgear Update
NETGEAR is aware of a security vulnerability that can potentially allow an attacker to slow or stop your network access. This vulnerability does not pose a risk for data loss or access to your network. This vulnerability potentially affects the following products:
* CM700
No workaround is available at this time.
NETGEAR is working to evaluate this vulnerability and will update this knowledge base article as more information becomes available.
At this point it’s beginning to feel like anything with a Puma 6 inside should probably be avoided, which is easier said than done for big ISPs like Virgin Media that take their orders from Liberty Global. Intel has long since moved on from the older Puma 6 but they’re still required to provide support to vendors, even if that support does appear to move at a snail’s pace.
Mark is a professional technology writer, IT consultant and computer engineer from Dorset (England), he also founded ISPreview in 1999 and enjoys analysing the latest telecoms and broadband developments. Find me on X (Twitter), Mastodon, Facebook, BlueSky, Threads.net and Linkedin.
« London Grid for Learning Raises Minimum Speeds for Schools to 100Mbps

















































Comments are closed